Posts by pwsadmin
Apple Unveils New iPhone 17 Lineup, Updated Apple Watches, and AirPods Pro 3
In the tech world, September brings the fruits of Apple’s harvest: new iPhones, Apple Watches, and AirPods. At its recent Awe Dropping event, Apple introduced the new iPhone 17 lineup, the ultra-thin iPhone Air, the Apple Watch SE 3, Apple Watch Series 11, Apple Watch Ultra 3, and the AirPods Pro 3. These are updates […]
Read MoreTen Tips for Making the Best Use of AI Chatbots
Since ChatGPT launched in late 2022, people have been using AI chatbots to brainstorm, speed up research, draft content, summarize lengthy documents, analyze data, assist with writing and debugging code, and translate text into other languages. Recently, the major chatbots have gained Web search capabilities, allowing them to access live information beyond their training model […]
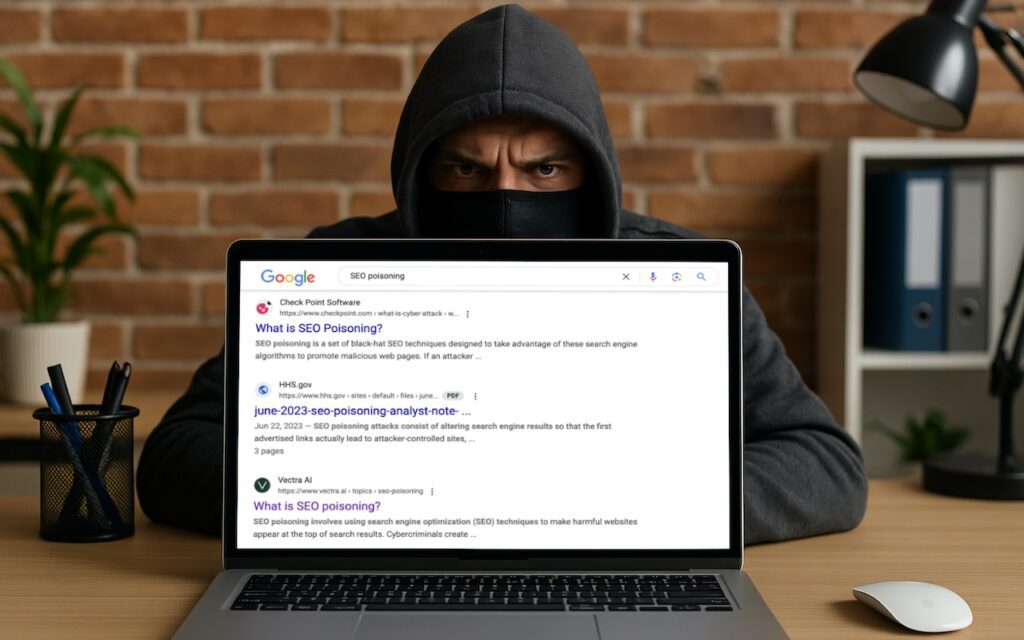
Read MoreDon’t Assume That Top Google Search Results Are Guaranteed Safe
We hate to encourage paranoia, but all is not well with Google Search. Recently, we’ve heard of multiple instances where people were nearly taken advantage of due to relying on the top result in a Google search. In one case, a user called a purported HP support phone number directly from the search results but […]
Read MoreWhy Passkeys Are Better than Passwords (And How to Use Them)
No one likes passwords. Users find managing them annoying, and website managers worry about login credentials being stolen in a data breach. The industry has developed a better solution: passkeys. Passwords versus Passkeys Traditional multi-factor authentication involves three methods of authentication, at least two of which are required for protection. They include something you know […]
Read MoreShare Wi-Fi Network Passwords Using QR Codes
A neat feature built into iOS, iPadOS, and macOS is that when you are connected to a Wi-Fi network, your devices will offer to share the Wi-Fi password if others near you try to connect to the same network. However, for this feature to work, they must be in your Contacts, and at times, it […]
Read MoreWhy Every Business Needs an AI Policy
Are employees at your company surreptitiously using artificial intelligence tools like ChatGPT, Claude, Copilot, and Gemini for everyday business tasks? It’s likely. An October 2024 Software AG study found that half of all employees use “shadow AI” tools to enhance their productivity, and most would continue using them even if explicitly banned by their employer. […]
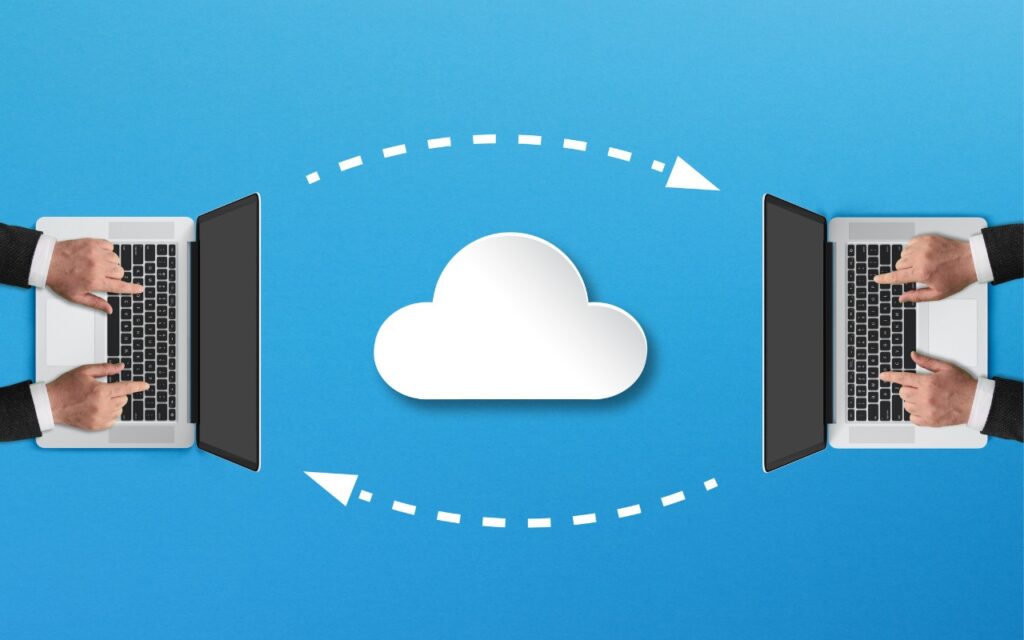
Read MoreTry Blip for Fast Transfers of Any Size Between Platforms
For file transfers, Apple users routinely rely on tools like AirDrop, Messages, email, cloud services, and public sharing websites, but these solutions can fall short when dealing with very large files, sharing across platforms, or confidential data. For such scenarios, Blip offers a reliable solution that works across Macs, iPhones, iPads, Android devices, Windows, and […]
Read MoreUse AirPlay to Mirror or Extend Your Mac’s Display
Apple’s AirPlay is one of those low-level technologies that’s more capable than many people realize. In addition to allowing you to stream video and audio from an iPhone, iPad, or Mac to an Apple TV connected to a large-screen TV, AirPlay also enables you to use that TV as an external Mac display, either mirroring […]
Read MoreMake Sure to Check Settings on Multiple Devices
We recently helped someone having trouble with 1Password requesting their password repeatedly on their iPad, but not on their iPhone. Since 1Password’s data syncs between devices, this person didn’t realize they needed to configure the app’s security settings separately for each device. It’s appropriate for 1Password to separate security settings—one device could be used in […]
Read MoreApple Silicon Macs Can’t Boot from the DFU Port
Booting from an external SSD (hard disks are too slow) provides a convenient way to test specific versions of macOS or troubleshoot problems with your Mac’s internal storage. However, a little-known gotcha has caused untold hair loss among those trying to boot from an external drive. Macs with Apple silicon cannot start up from external […]
Read More